Surveillance Capitalism with Chinese Characteristics? Trade, Financing, and Technological Lock-In in Africa and Southwest Asia

China incessantly expands exports of surveillance technology to Africa and Southwest Asia. In the absence of a robust regulatory framework, partner countries risk sliding into surveillance capitalist exploitation – feeding Chinese tech giants without adequate recompense. Cross-border data flows are perhaps the most vulnerable aspect of such new interdependencies, which the EU must navigate in an increasingly fragmented global data order.
China’s Expanding Security Footprint
Fresh analysis of newly uncovered evidence suggests that China’s foreign police-training effort is far larger and more extensive than previously understood. Through partnerships with security agencies in at least 138 countries, Beijing is deepening its engagement with foreign law-enforcement systems. These efforts are particularly visible in Southwest Asia and North Africa, where governments facing digital infrastructure gaps are increasingly reliant on external surveillance and security technologies.
Under the Global Security Initiative, Beijing is not merely exporting training programs but an integrated security model. As Chinese security agencies work with counterparts in 138 countries, systems of technologically enabled social control increasingly travel alongside China’s commercial surveillance technologies. This trajectory resembles what Shoshana Zuboff describes as “surveillance capitalism,” in which human experience is captured and converted into data designed to anticipate and influence behavior – a logic that, in this case, is intertwined with China’s state-led security exports.
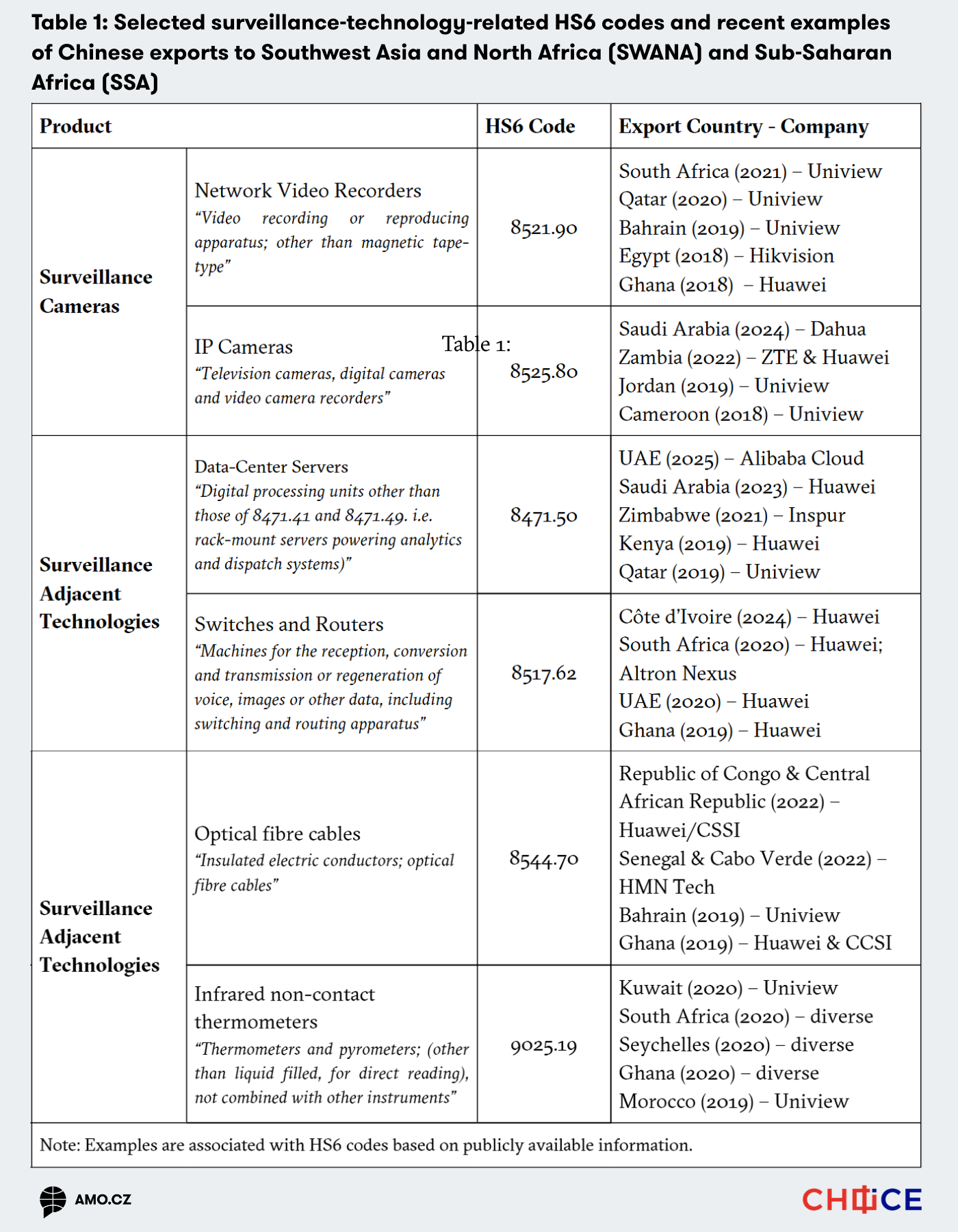
Beijing’s technology companies play a central role in this process, particularly through their expansion into Southwest Asia and North Africa. Many governments in these regions (including South Africa, Zimbabwe, and Ghana) confronting acute digital infrastructure deficits, have turned to Chinese surveillance technologies ranging from expansive facial-recognition camera networks to cloud-based data management systems and complementary software services. Table 1 shows an overview of recent examples of surveillance technology exports of Dahua, Hikvision, Huawei, and others. We also associated the exported products with the global codification system under which they are classified by customs offices (HS6 codes), for further analysis below.
Notably, these exported packages often include opaque data-processing capabilities. Past incidents – such as the alleged backdoor in the African Union’s (AU) data center – highlight concerns that information could be transferred beyond national borders and deepen dependencies on China’s digital ecosystems. Thus, while these technologies promise enhanced security and administrative efficiency, they also introduce significant risks, particularly for countries lacking robust data-protection laws.
Trade, Financing, and Strategic Economic Penetration
Often subsidized by soft loans from the Chinese Exim Bank, such technologies serve first and foremost as tools of strategic economic penetration, reflecting a pattern in which China lends not to the poorest or most distressed countries, but to resource-rich, creditworthy states, using favorable credit terms to deepen long-term influence over critical infrastructure and markets. These imports are part of both single initiatives and broader projects such as the Digital Silk Road (DSR) – a key component of China’s Belt and Road Initiative (BRI) – an ambitious project aimed to enhance telecommunications networks, artificial intelligence capabilities, cloud computing, e-commerce and mobile payment systems, surveillance technology, smart cities, and other high-tech sectors in the recipient countries. Given the close ties between Chinese companies and the Chinese Communist Party (CCP), these companies appear to be refining surveillance capitalism on a global scale, acting as the extended arm of China’s broader surveillance agenda.
Driven by state security needs, the desire for enhanced political stability, and the opportunities provided by digital technologies, some Global Majority countries – that is, countries outside Western Europe, North America, Japan, Australia, and New Zealand (hereafter referred to as “Minority World countries”) – have become significant recipients of Chinese surveillance technology exports. Their demands are primarily, though not exclusively, addressed through initiatives such as Smart City and Safe City projects, which integrate advanced technologies to improve administrative efficiency, automate key services, enhance public safety, and enable the detection and prevention of criminal or harmful activities.
State Support, Strategic Financing, and Market Dominance
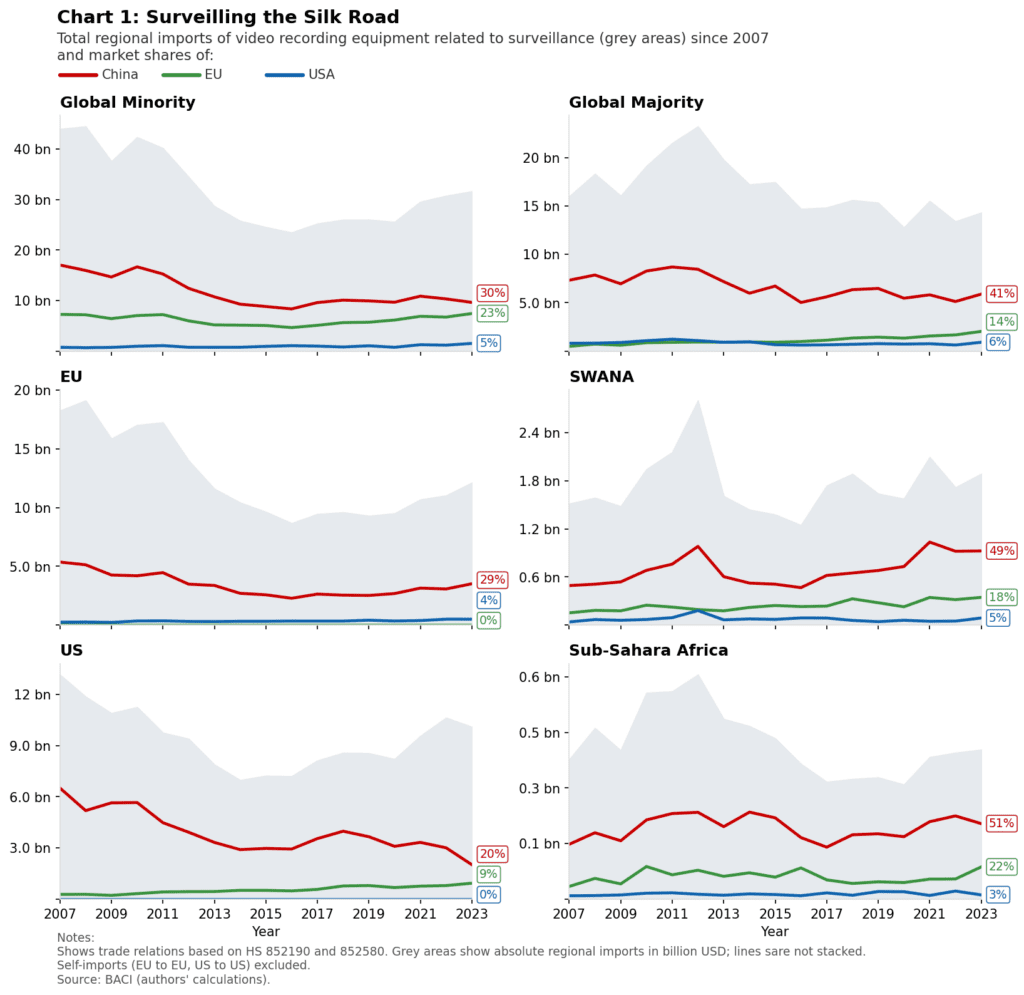
As a matter of fact, China stands out as the economy that allocates the highest share of its GDP on industrial support among major economies. In 2023, China’s support for its industries amounted to at least 4.4 percent of its GDP. The combination of soft loans, industrial support, and urban surveillance suites effectively meets the needs of many African and SWANA countries. This alignment results in the pattern displayed in Chart 1 below. Imports of surveillance technologies from China to these regions are markedly higher than those from Europe or the US, revealing the effectiveness of China’s policy framework in translating strategic support into tangible economic and political influence.
For instance, in 2023, Chinese exports accounted for 51 percent of surveillance technology imports in Africa and 49 percent in SWANA, compared with only 22 percent and 18 percent from the EU and 3-5 percent from the US, respectively. An important contextual factor is the shifting global demand for surveillance equipment during the 2010s. While Minority World countries reduced their purchases as the counterterrorism-driven demand of the post-9/11 years diminished, SWANA and SSA countries were confronting heightened political mobilization and color-revolution-influenced unrest, which likely contributed to the spike in imports around 2011.
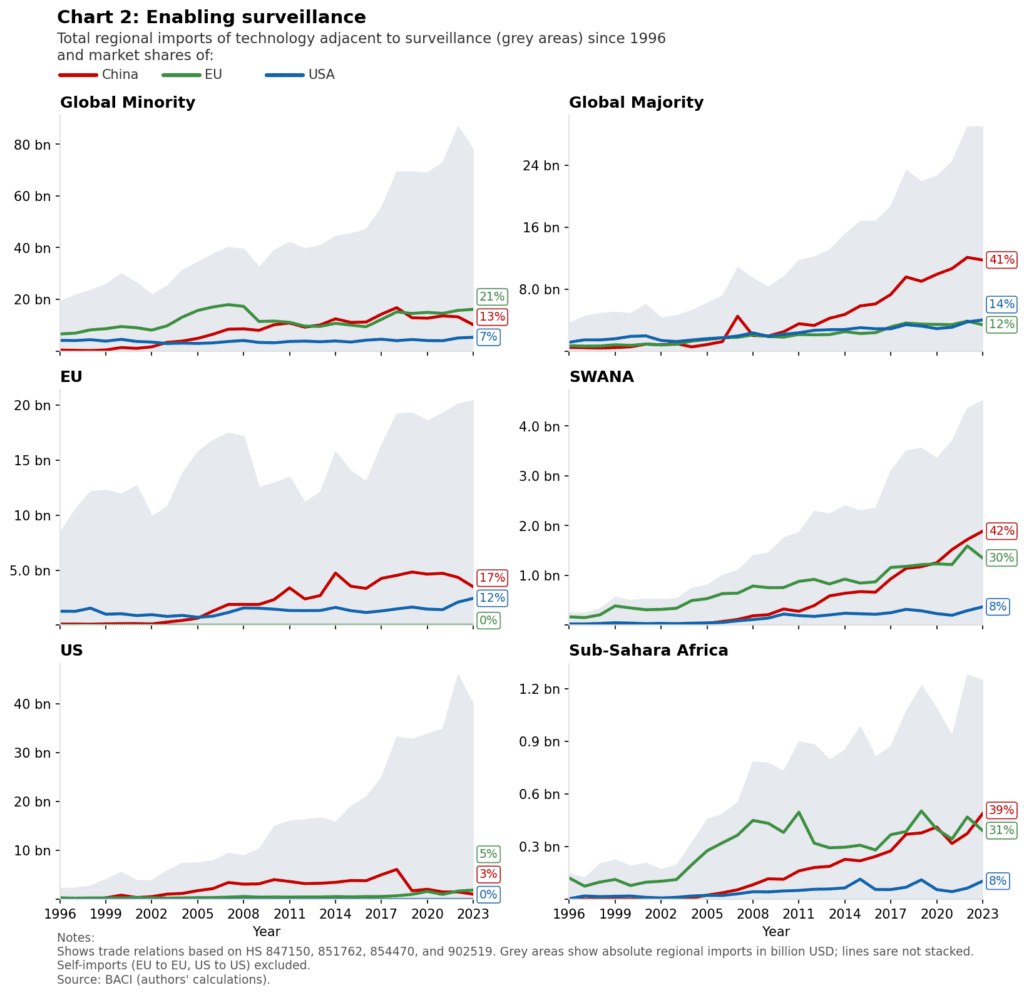
Entrenching Technological Dependence Through Infrastructure Lock-In
On top of that, as Chinese tech companies become increasingly involved and, in some cases, lead the technological development in Africa and the SWANA region, they also gain a competitive advantage. Companies like Huawei and ZTE, for instance, have strategically positioned themselves to secure future network upgrade contracts and provide complementary services, thereby fostering a growing dependency on Chinese technology systems in the contracting countries. This trend is reflected in imports of technologies related to surveillance infrastructure (such as processing units and networking equipment) which are, on average, significantly higher in African and SWANA countries than in the rest of the world.
Data Governance, Sovereignty Risks, and Legal Exposure
Concerns over data-gathering practices through surveillance technologies have intensified, particularly following allegations in 2017 that China exploited a backdoor in the computer network it had built at the AU headquarters in Ethiopia. It was revealed that sensitive AU information was being covertly transferred to servers in Shanghai, a discovery made after the AU’s IT team noticed unusual data transfers occurring nightly between midnight and 2AM, even when the offices were empty.
These concerns are further heightened by China’s National Intelligence Law, enacted in June 2017, which underscores the extensive reach of the CCP into Chinese telecommunications and other Chinese-owned and operated companies worldwide. Article 7 mandates that both organizations and citizens support and cooperate with national intelligence activities, placing them at the service of state surveillance efforts. Similarly, Article 22 of the 2014 Counter-Espionage Law allows state security organs to guide and inspect entities for potential espionage risks.
In addition to concerns about state access to data, racial bias in surveillance technologies, particularly in facial recognition systems, has emerged as a significant issue. A study by MIT’s Media Lab revealed that facial recognition technology often struggles to differentiate non-white faces accurately. To address this flaw, Chinese firms have been expanding into African markets to better train their algorithms. For example, in March 2018, Zimbabwe signed a contract with the Chinese startup CloudWalk Technology to roll out a nationwide facial recognition program. Through this partnership, supported by China’s BRI, Zimbabwe may be giving away valuable citizens’ biometric data. However, this issue extends beyond Zimbabwe, reflecting a broader trend across Africa where the rapid adoption of cutting-edge surveillance technology often outpaces the development of legal safeguards, leaving the door open for potential exploitation of sensitive data.
The EU in a Fragmenting Data Governance Landscape
The vulnerabilities exposed across Africa and Southwest Asia should also be understood in the context of an increasingly fragmented global data order. Rather than converging around a single set of digital governance norms, the international system is evolving toward parallel and, in some cases, incompatible data regimes, ranging from market-driven models to state-centric approaches to surveillance and control.
In this environment, Africa and Southwest Asia occupy a pivotal position: they are among the fastest-growing digital markets, yet remain institutionally underprepared to shape the governance terms under which new infrastructures are deployed. The large-scale diffusion of Chinese surveillance technologies in these regions, therefore, has implications that extend well beyond bilateral influence. Surveillance infrastructures anchor technical standards and legal assumptions that shape how data moves across borders and how authority over that data is exercised. Once embedded, such systems contribute to the consolidation of governance models that may prove difficult to reconcile with alternative regulatory frameworks.
For the EU, this trajectory matters because the viability of its own data-protection and digital-market rules increasingly depends on global interoperability, rather than internal coherence alone. If large parts of Africa and Southwest Asia become integrated into digital ecosystems governed by standards that are increasingly incompatible with European regulatory frameworks, the EU risks seeing its regulatory model geographically confined, even as global data flows continue to pass through and around its jurisdiction. Against this backdrop, the implementation of the African Continental Free Trade Area’s Digital Trade Protocol (DTP) marks a significant step toward regional data governance. By articulating common rules on cross-border data flows, data localization, and digital trade facilitation, the DTP offers a potential foundation for a more coherent and autonomous African digital space, one that could, in principle, remain interoperable with the EU’s regulatory framework.
Written by
Alessia Noschese
Alessia Noschese is a Master’s student specializing in international security at the Hertie School in Berlin, and a FORESIGHT Lab Fellow at the Aletheia Research Institution.
Kai von Carnap
kavocaboKai von Carnap is a Research Associate as part of the project “Digital Sovereignty of Europe (DigitS EU)” at the University of Trier. He is pursuing a PhD where he focuses on global internet governance and the interplay between digital technologies and state power. He is also an Associate Fellow at the Center for Geopolitics, Geoeconomics, and Technology at the German Council on Foreign Relations (DGAP), as well as a BLOCS Lab Fellow at the Aletheia Research Institution.